Mikrotik devices and cloud routers are targeted by a mass botnet attack
Recent reports raised attention on a botnet spreading around, targeting Mikrotik RouterOS devices and Cloud Routers by exploiting vulnerabilities in HTTP and SMB, as well as password brute-forcing.
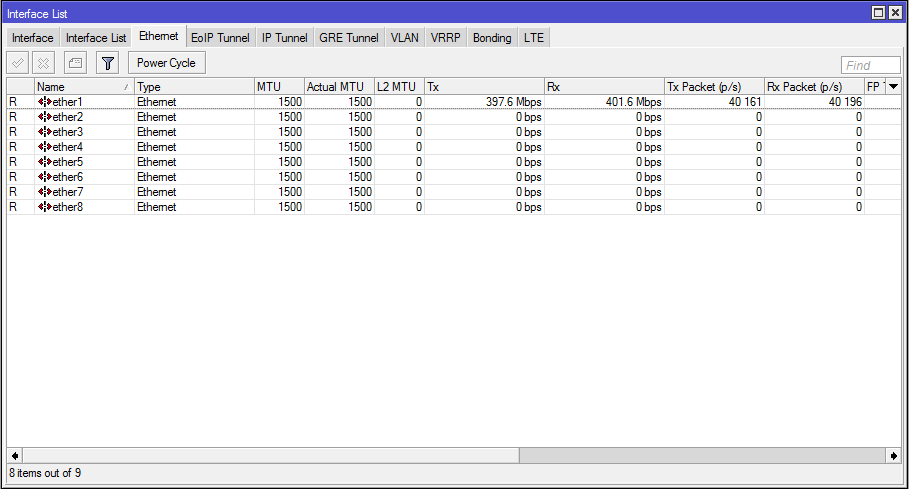
The worm tries to locate Mikrotik devices by an massive and aggressive scanning for TCP port 8291 (Mikrotik Winbox interface). If it finds a potential target it tries to exploit the know security hole in the HTTP and SMB implementation. The botnet also tries to brute-force detected Mikrotik devices and eventually neighbors of infected devices.
Most reports claim that exploits are most successful on outdated OS versions like the v6.38.4 and older, but as part of the attack is a simple combination of port scanning and brute-forcing this cannot be fully categorized as a vulnerability exploit.
Recommendations
The best approach is to always firewall management interfaces. Our recommendations are:
- firewall Winbox TCP port 8291, SSH and HTTP ( especially if Mikrotik Webfig is available )
- disable SMB (it might be an attack vector)
- disable Telnet (attack vector for brute-forcing)
- update RouterOS to latest stable version
Keep your devices and Cloud Routers OS up to date. Latest stable version 6.41.3 is reported as less vulnerable in terms of the HTTP exploit.
Update 29.03.2018:
Although the attack is not sophisticated it seems to spread very well. New data shows that infected devices try to to brute-force neghbors mostly on Telnet interface.
Most infected devices are older versions, although the most common pattern is devices with telnet or webfig interfaces left open.